WPY Data
Cybersecurity and Privacy Risk Management
Couldn't load pickup availability
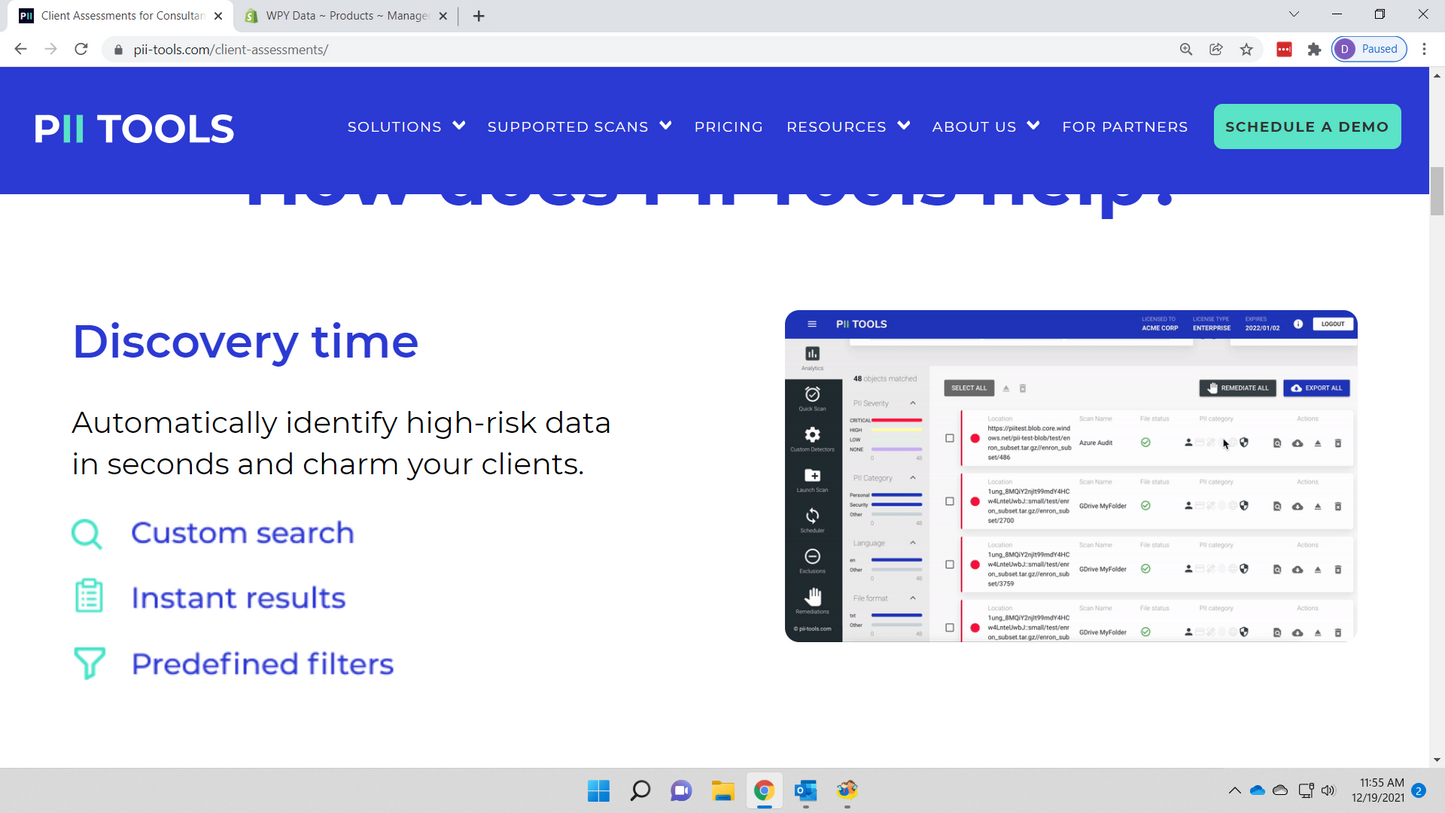
WPY Data utilizes internal data to measure an organization's operations against its risk tolerance. Our platform provides real-time updates to key risk indicators and presents reporting in a way that is easily understandable for both management and the board.
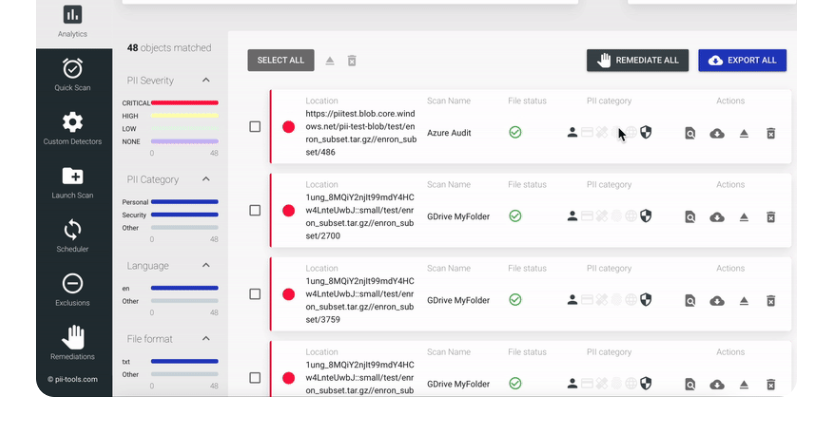
The WPY Data Key Risk Indicator (KRI) dashboard utilizes security operations data to create 16 KRI’s in a way that is easily understood by management and the board. The dashboard improves communication and collaboration across the organization. Allowing more informed decision-making and a better understanding of the organization's overall risk profile.
The WPY Data KRI dashboard is essential for any organization that wants to effectively manage its cybersecurity and privacy risks. By having a centralized source of data that is continuously updated, the organization can quickly identify potential risks and take action to mitigate them. This can help prevent data breaches and other cybersecurity incidents that can be costly both in terms of financial losses and damage to the organization's reputation.
Share